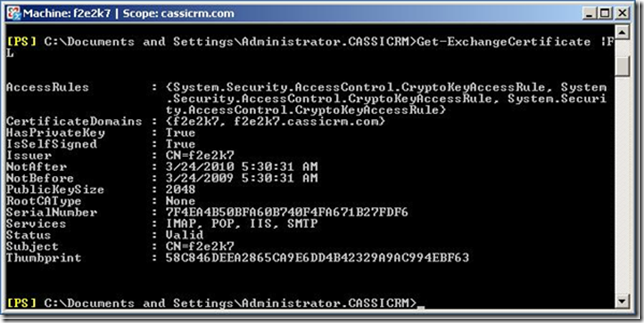
When a new Exchange Server 2007 role is installed on a computer the server automatically generates a self signed certificate to be used with services like transport (SMTP), POP, IIS (OWA and Exchange Web Services) and IMAP. This certificate expires right after the completion of one year from the date server was installed or the certificate was reassigned manually. To check the status of the certificate using Exchange Management Shell. Executing the cmdlet Get-ExchangeCertificate |FL displays all relevant information about all the certificates assigned, enabled and being used or not used by Exchange Services.
You may see more than one certificate listed on your exchange server(s) and that may be simply because you or someone else from your team have already tried working with certificates on the server.
If you see the above picture, you will notice that the certificate I have on my server is valid till 24th March 2010. NotAfter holds the value in mm/dd/yyyy h:mm:ss format. NotAfter – means this certificate will not be valid after the time stamp listed in this field. On the other hand the value NotBefore – means that this certificate will not be valid before the time stamp mentioned.
So once you cross the date listed in field NotAfter the certificate becomes invalid and indeed may open up doors to many other troubles like connectivity to web services, SMTP transport, POP and IMAP retrieval, etc. To renew the certificate you can simply run a cmdlet and get a new self signed certificate. But, this is just not as simple as simply running a cmdlet and get a new certificate, there is a procedure to do it. Check the following steps:
1. Run Get-ExchangeCertificate |FL – This will list details of all certificates that you have assigned to Exchange Services. Please understand, this cmdlet does not retrieve any information about any other certificate from local certificate store which is not used by Exchange. Once you get the output printed on the screen; note down the Thumbprint of certificate into a notepad.
2. Run Get-ExchangeCertificate –Thumbprint “58C846DEEA2865CA9E6DD4B42329A9AC994EBF63” | New-ExchangeCertificate . This renews the certificate. You will notice the moment you press enter on keyboard you may be prompted to confirm if you want to use the same certificate for SMTP service.
3. Check if the certificate is renewed. This can be simply examined by looking at the changes in thumbprint of the certificate after running the cmdlet mentioned in step 2. You can see the changed thumbprint in below picture.
4. Looking correctly to the above picture you will also notice that the certificate is not being used to secure IIS based services anymore though the NotAfter and NotBefore dates have changed. To enable this renewed certificate for IIS as well run Enable-ExchangeCertificate – Thumbprint “E0BB201793DC74D0F94F3275E6AA53BA75907565” –Services IIS
5. Verify all the services are working correctly after renewing and enabling the certificate.
6. Remove old certificate by running Remove-ExchangeCertificate –Thumbprint “58C846DEEA2865CA9E6DD4B42329A9AC994EBF63”


Keine Kommentare:
Kommentar veröffentlichen